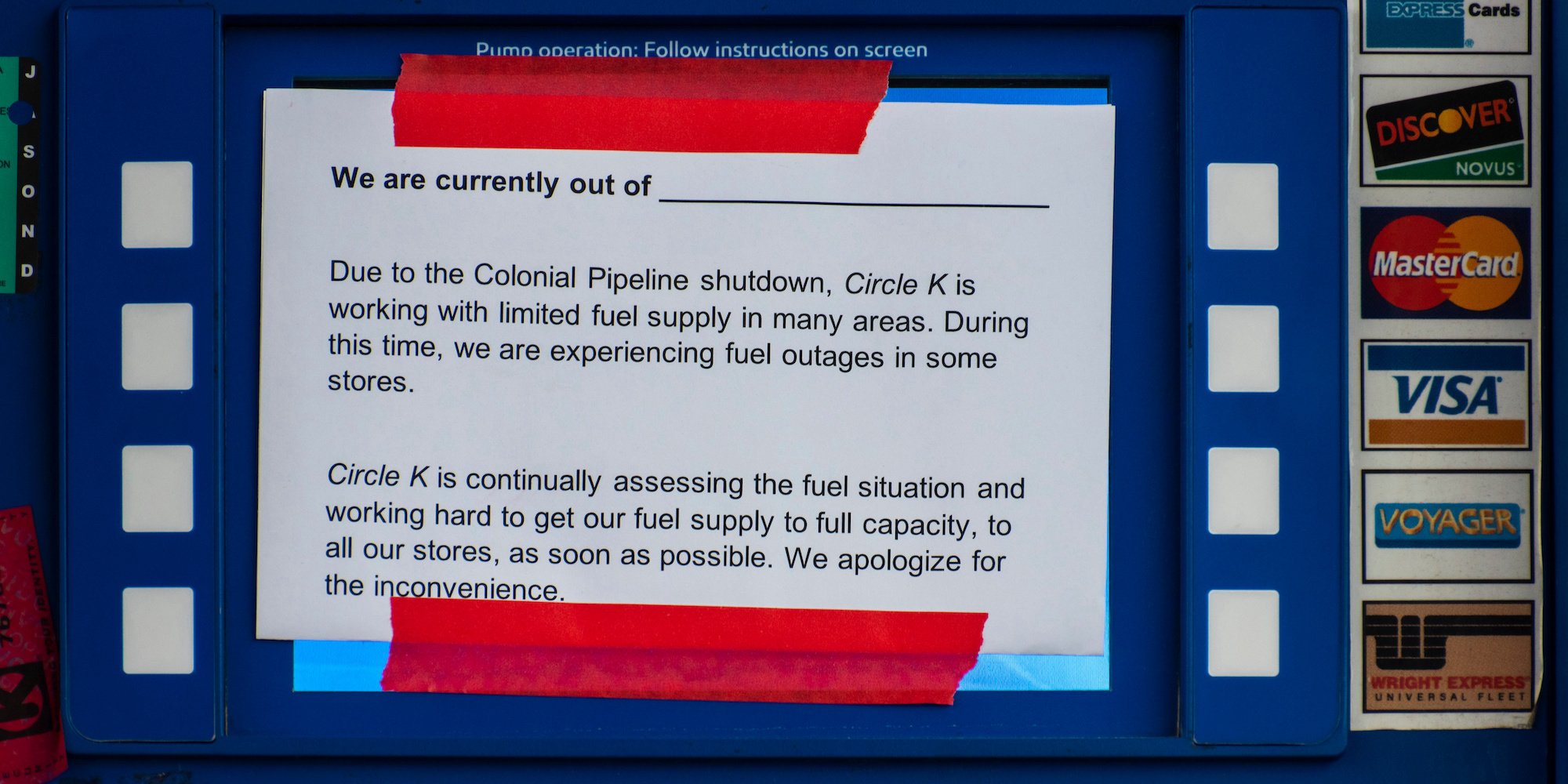
Few need to be reminded of the fears that the Colonial Pipeline hack caused in May of 2021, in which airlines scrambled to keep their planes fueled for long-haul flights and Americans across the eastern seaboard panic-bought gas in expectation of supply disruptions.
The severity of the Colonial Pipeline attack was a wake up call for cybersecurity industry leaders, government officials and the media. But speaking at the Black Hat Briefings conference last week, Kim Zetter, an award winning cybersecurity journalist, said that the private sector and the federal government should have seen the attack coming.
Zetter, whose 2015 book Countdown to Zero Day provided the most thorough accounting to date of the Stuxnet worm attack on Iran’s nuclear enrichment facility at Natanz, used a keynote speech at this week’s Black Hat Briefings in Las Vegas to declare the Colonial Pipeline hack “foreseeable,” pointing to countless warnings given by government entities and cybersecurity experts on the high probability of attackers targeting these entities.
25 years of alarms on critical infrastructure cyber risk
And many of those warnings are not of recent vintage. For example, Zetter cited a 1997 warning by U.S. Federal Government officials about possible cyber attacks on critical infrastructure (CI). In October of 1997, President Clinton’s Commission on Critical Infrastructure Protection emphasized the “increasing vulnerability of control systems to cyber attacks.” The Chairman of this same Commission wrote to the President in their report that the “capability to do harm–particularly through information networks–is real (…) and we have little defense against it.”
Colonial's cybersecurity is the norm, not the exception
Despite that, the state of America’s CI has not changed drastically over the past 2 decades, with the American Society of Civil Engineers giving America’s CI a “C-” grade in 2021. The capabilities of cybercriminals have improved as a result of vast advancements made in technology generally. What hasn’t changed over the years is these same criminals’ desire to target CI entities.
In fact, there were specific warnings about pipeline hacks. Zetter mentioned that in February of 2020, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) released an alert warning CI operators of the possibility of ransomware impacting pipeline operations. The alert came as a result of a cyberattack that affected the “control and communication assets on the operational technology (OT) network of a natural gas compression facility.” The infamous Colonial Pipeline hack happened just 15 months later.
While Zetter pointed out several examples of Colonial Pipeline lacking proper security measures that contributed to this attack happening, such as having no company CISO at the time of the attack, she made it clear in her keynote that the Colonial Pipeline incident was no exception. She stressed that this incident is “a convenient example” to draw from, but that “other critical infrastructure is in the same position, or worse.”
The lesson from the Colonial Pipeline hack, Zetter said, is to "mind the gap" between the best practices advocated by cybersecurity professionals and what critical infrastructure owners and operators actually implement. Many protective measures that professionals have cited as necessary in an attempt to secure CI have not been implemented, despite more than twenty years of warnings.
With the private and public sectors consistently lacking “imagination, or anticipation about the next move hackers will make,” the advantage remains solidly with the attackers, Zetter said.