Spectra Assure Free Trial
Get your 14-day free trial of Spectra Assure for Software Supply Chain Security
Get Free TrialMore about Spectra Assure Free Trial
The January 2023 update improves file and report storage options for Microsoft and Amazon Web Services (AWS) platforms, as well as appliance management for SOC Administrators and other users.
ReversingLabs Elastic Threat Infrastructure (TitaniumScale) helps enterprises baseline the security of their environment, assessing millions of files per day to quickly find and prioritize threats for remediation. It uses unique ReversingLabs File Decomposition Technology to extract detailed metadata, add global reputation context and classify threats. It automatically acquires files by integrating with shared drives, email gateways, intrusion detection systems, firewalls and other devices. Results feed into analytics platforms to provide visibility and enriched data for remediation and advanced hunting.
ReversingLabs Elastic Threat Infrastructure provides value in a number of ways. Organizations can improve their security posture by reducing cyber risks, while also ensuring data and file privacy. Additionally, they are able to decrease operational workload and tool costs. And equally important, practitioners benefit from using our solution's advanced technology, which reduces MTTD by prioritizing malicious files for triage.
In this enhanced version of ReversingLabs Elastic Threat Infrastructure, several updates have been made to improve file and report storage options for Microsoft and Amazon Web Services (AWS) platforms, as well as appliance management for SOC Administrators and other users.
Below, we break down these major product updates for you.
Building on the solution’s threat detection and analysis support of Microsoft Cloud Storage (OneDrive and SharePoint Online), users now have the option to save files, extracted files and reports to the same OneDrive folder or SharePoint Online (SaaS) site from which files were processed and classified, improving file analysis and coverage.
SOC teams have more flexibility to organize unclassified and classified files in their OneDrive or SharePoint Online platform, without the need to use another storage platform for files that have been processed. This also gives users a better means for sharing files and reports with other SOC analysts and team members.
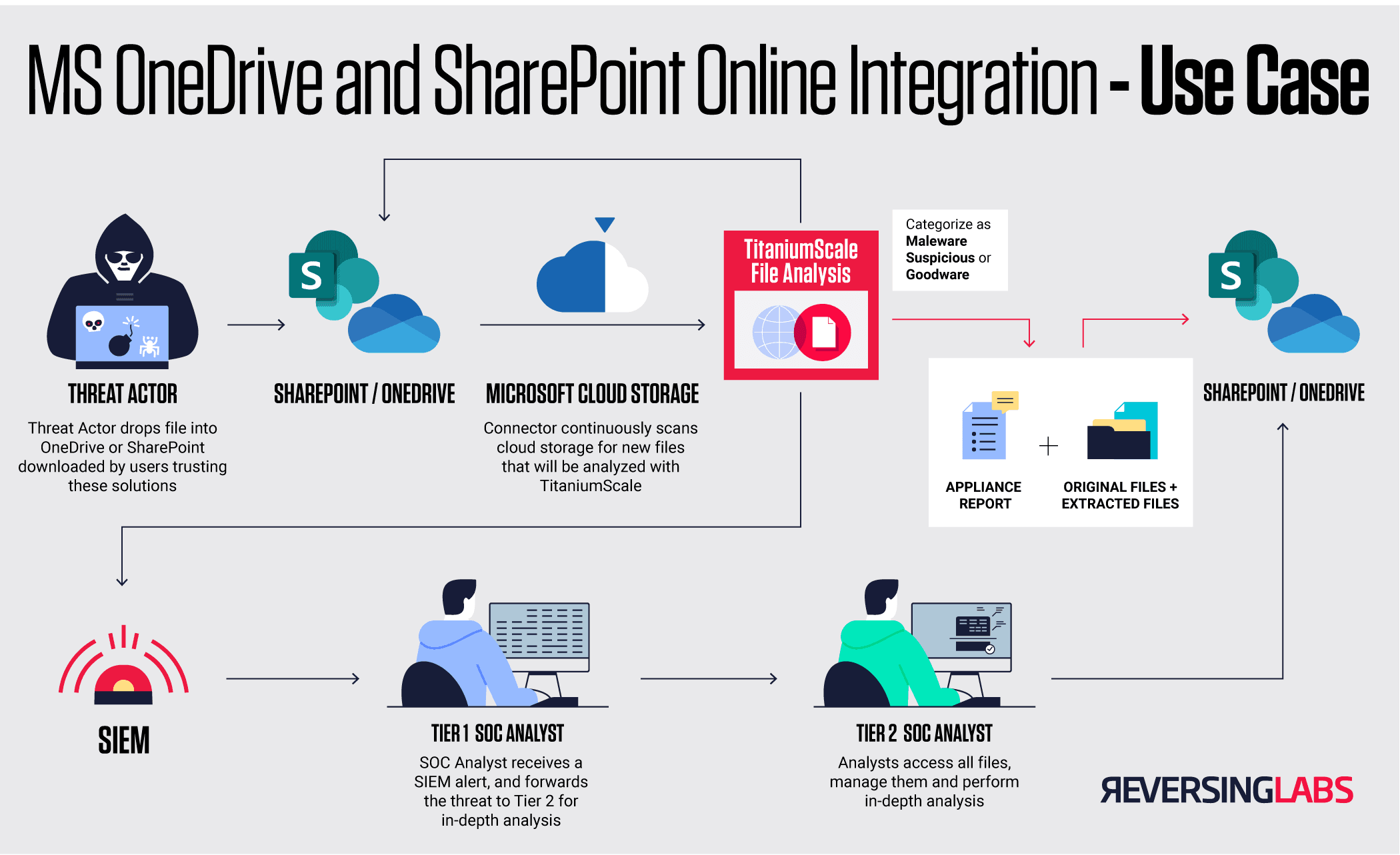
Figure 1. TitaniumScale file scanning flow with OneDrive and SharePoint
AWS S3 users as well as S3-compatible storage users have more flexibility on where to store their file analysis reports with the latest ReversingLabs Elastic Threat Infrastructure release. SOC administrators have a choice to store reports in a default S3 bucket, the input bucket from which the processed file originated, or choose more than one output location for these reports by mapping output to input buckets. The administrator can determine where a report should be stored based on ease of access for themself as well as other users in the organization.

Figure 2. Report storage options for AWS and S3-compatible storage
At ReversingLabs, we understand that SOC administrators have many responsibilities to juggle, which means saving time is important. Based on customer feedback, we’ve centralized management of appliances on one screen to improve ease of use and system performance. We’ve also added appliance Type and Version columns for version control, and a simple way to copy IP addresses for updates. Administrators can more easily troubleshoot appliance issues with the addition of system health metrics available on the Central Manager Appliance Management tab.
This redesign greatly benefits our customers by giving users an ease of administration and better usability, thanks to an overall improved user interface.

Figure 3. Centralized appliance management
ReversingLabs will continue to enhance the Elastic Threat Infrastructure solution, so that organizations can continue to bolster their robust programs to can help mitigate today’s most serious malware threats.
New updates to this solution, such as Microsoft Cloud Storage integration, more file and report storage options, and a redesigned appliance management system improve work efficiency so users can complete tasks more efficiently.
ReversingLabs is the leading provider of explainable threat intelligence solutions that shed the necessary light on complex file-based threats for enterprises stretched for time and expertise. Its hybrid-cloud Titanium Platform enables digital business resiliency, protects against new modern architecture exposures, enables software risk verification, and automates manual SOC processes with a transparency that arms analysts to confidently take action.
ReversingLabs is used by the world’s most advanced security vendors and deployed across all industries searching for a more intelligent way to get at the root of the web, mobile, email, cloud, app development and supply chain threat problem, of which files and objects have become major risk contributors.