Spectra Assure Free Trial
Get your 14-day free trial of Spectra Assure for Software Supply Chain Security
Get Free TrialMore about Spectra Assure Free TrialSoftware buyers are demanding that the products they acquire are safe and secure. They also expect transparency from providers when it comes to software provenance, composition, and authenticity. Meanwhile, threat actors are targeting software producers using increasingly sophisticated tactics to infiltrate the software development process. By quietly injecting malware, tampering with build systems, or compromising third-party services, they aim to turn your own software releases against you and attack your customers.
High-profile supply chain breaches like SolarWinds, 3CX, and Notepad++ prove that the biggest threats don’t always come from open source code. Industry leaders and governmental entities have taken notice, with CISA formalizing a Secure by Design philosophy that shifts security responsibility from end users to software manufacturers and OWASP adding Software Supply Chain Failures to its iconic Top 10 Most Critical Web Application Security Risks.
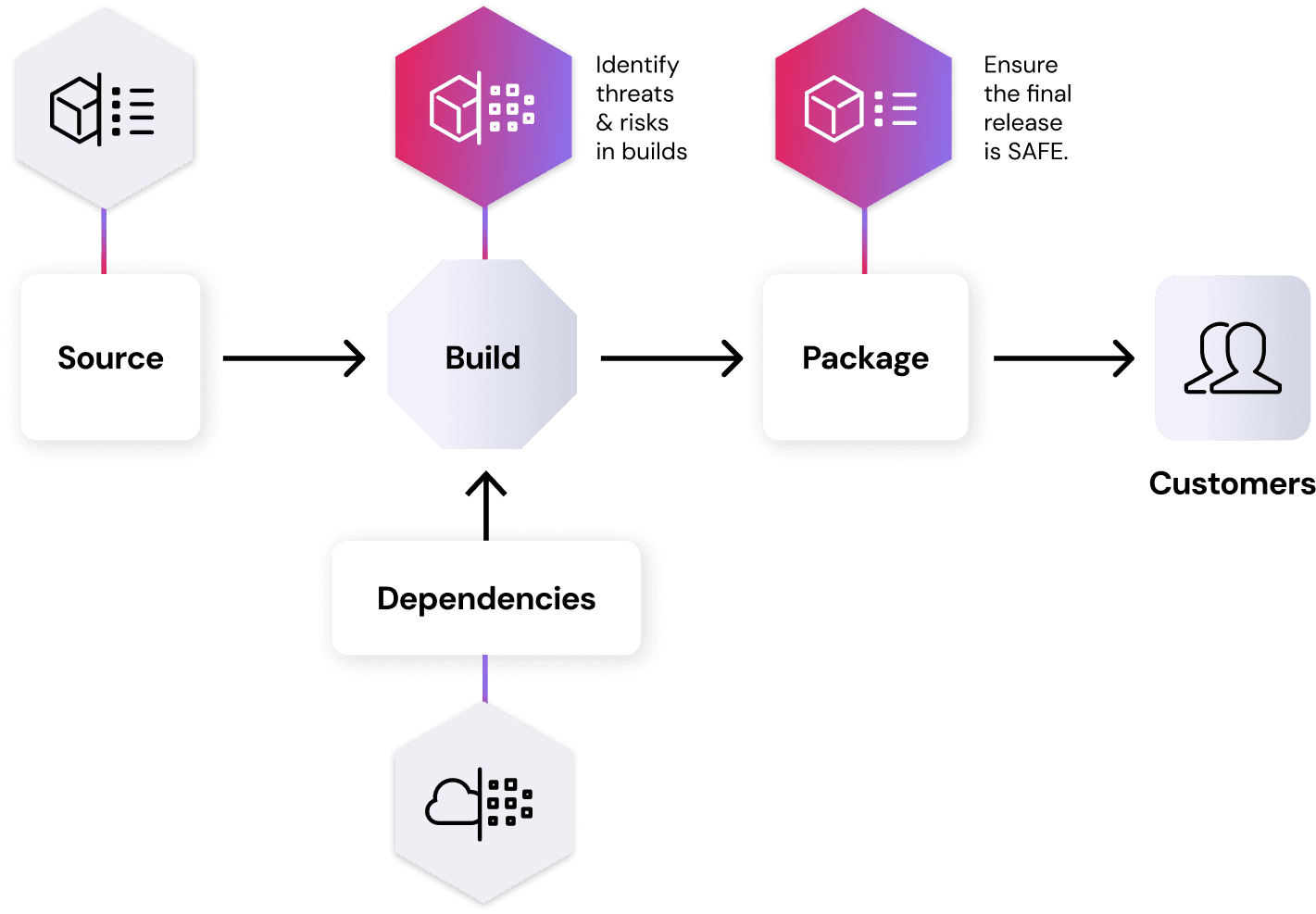
Use Spectra Assure to verify the safety and integrity of your software releases, protecting your business and customers from supply chain attacks. Identify hidden malware and malicious code tampering through a post-build binary scan – the essential final exam for your releases. Why scan the final, assembled binary? The same reason that vehicles are crash-tested. It’s critical to understand how the finished product performs in its final, integrated state, not just how the individual parts perform.
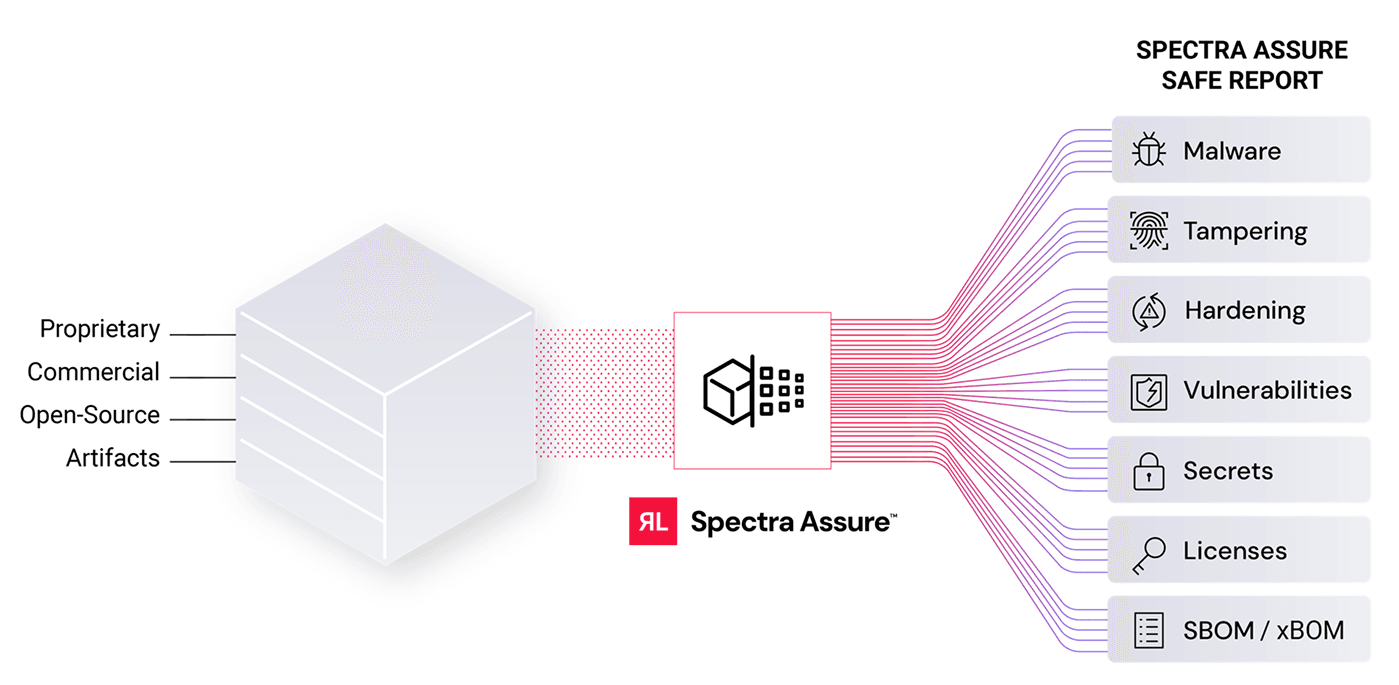
Spectra Assure performs a deep analysis that recursively deconstructs every layer, uncovering embedded files and hidden risks that other tools miss. Our comprehensive SAFE report details everything from malware and tampered code to vulnerable dependencies, suspicious behaviors, and leaked secrets. Broad file support means that virtually any software package can be analyzed – from containers and virtual machines to Windows installers, Linux binaries, and AI models. Your preferred policies are applied instantly to know if your standards are met.
Protect against a wide range of software supply chain attacks with automated threat hunting, differential analysis, and reproducible build analysis.
Defend against vulnerable or malicious open source and third-party components sneaking into your releases at build time.
Rest easy knowing that your software releases are thoroughly tested for a wide range of security risks, keeping your customers safe.

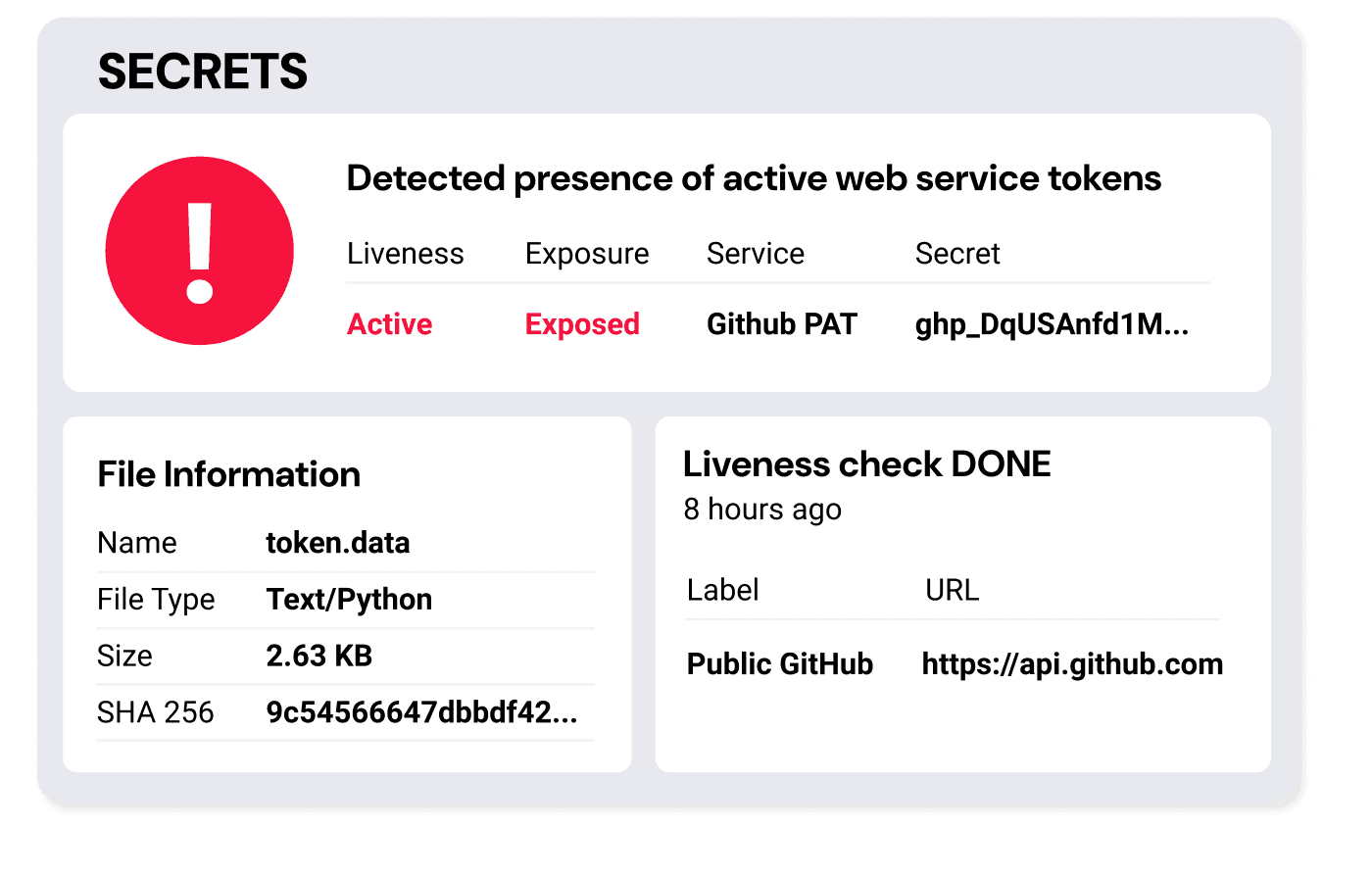
Prevent malicious supply chain attacks that aim to expose secrets or source code and protect your company’s IP and brand reputation.
Attacks like the Shai-hulud worm underscore the importance of protecting against leaked secrets and exposed source code.
By confirming the integrity of software releases, your brand is safe from the potentially catastrophic fallout of a supply chain compromise.
Leverage security and transparency as a market differentiator to accelerate sales cycles.
Demonstrate to customers that your releases undergo a rigorous and verifiable set of safety checks with Spectra Assure.
Turn compliance into a competitive advantage with detailed xBOMs that meet industry standards. Both CycloneDX and SPDX are supported, including SBOM, AI/ML-BOM, SaaSBOM, and CBOM.
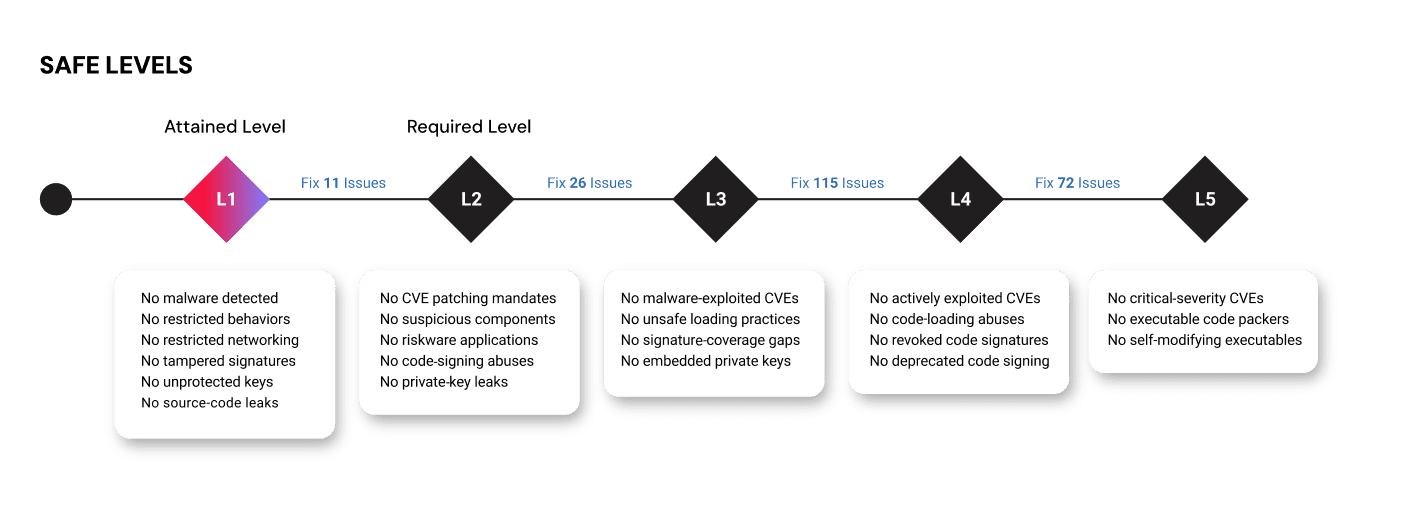
Continuous quality insights create a feedback loop that consistently elevates your software standards.
Quantify your progress with SAFE Levels: A tiered roadmap that systematically raises software quality and brings comfort to your customers who know they are working with a partner committed to product security.
Use AI-coding assistants confidently. We ensure the building blocks they suggest are safe.
Spectra Assure uses proprietary detection technologies, explainable machine learning (ML), and an extensive file reputation database of over 40 billion files to detect file tampering and prevent software supply chain attacks.
Through deep analysis of the software binary in its final, shipped form, software publishers can uncover embedded files and hidden risks that other tools miss, ensuring there are no surprises for your customers.
While others provide a list of CVEs in open-source components, Spectra Assure delivers clear, actionable insights across a comprehensive set of assessment categories that can be fine tuned to align with your organizational risk tolerance.
Built-in differential analysis between versions tracks improvement in software quality, while checking for suspicious changes and indicators of tampering that match past supply chain attacks.


A compromise of the source code editor underscores attack method diversification. It's time to go beyond trust.


Binary analysis is a must-have control for securing third-party software, before installation.