Spectra Assure Free Trial
Get your 14-day free trial of Spectra Assure for Software Supply Chain Security
Get Free TrialMore about Spectra Assure Free Trial
With thousands of published modules available for use, PowerShell Gallery is as essential to Windows automation as npm is to JavaScript development. System administrators and DevOps professionals depend on shared modules to automate tasks, manage cloud resources, and streamline their workflows. However, this widespread adoption and open access also make it an attractive target for malicious actors seeking to compromise enterprise environments.
While attacks on open source repositories like npm, PyPI, and RubyGems frequently make headlines, malicious actors are increasingly targeting less well known public repositories. IT automation scripts are not typically perceived as a potential source of compromise, however, like most scripting languages, PowerShell can enable command hijacking and clobbering techniques that attackers can exploit and are also difficult to detect.
Although the PowerShell Gallery site states that community content should be regarded as inherently untrusted, many administrators install PowerShell modules directly from the Gallery, making it easier for malware to slip through undetected. What used to require an elaborate attack path is now trivial. The simplicity of PowerShell Gallery’s Install-Module command allows adversaries to deliver malware in one step.
The fact that PowerShell modules are easy to install, execute with elevated privileges, and provide pervasive access to Windows resources, make them a prime target for supply-chain attacks. To adequately protect themselves, enterprises must implement a preventative control to evaluate these modules before approving them for use.
[ See PowerShell Gallery research post | Guided tour: Spectra Assure Community ]
Spectra Assure Community now empowers PowerShell users to verify a module's level of risk before trusting it to run with privileged system access. The free-to-use, no-registration-required platform provides comprehensive risk assessments for thousands of modules published to the Gallery. The simple search interface enables any system administrator, DevOps engineer, or IT security specialist to make more secure choices for their automation workflows.
Each assessment summarizes supply chain risks and threats such as malware, tampering, exposed secrets, and vulnerabilities. Information on package activity, popularity, and contributors helps to identify unsupported and outdated modules and dependencies. The number of removal incidents occurring in the last two years can provide insight into ongoing security challenges with the module or indicate the contributors’ diligence to improve software safety.
The assessment also includes a list of direct dependencies, which is exportable in CycloneDX format, and provides links to Spectra Assure's assessment of the listed open source dependencies. Users can also examine the list of software behaviors exhibited by each module to identify anomalous or unnecessary capabilities that could indicate malicious intent.
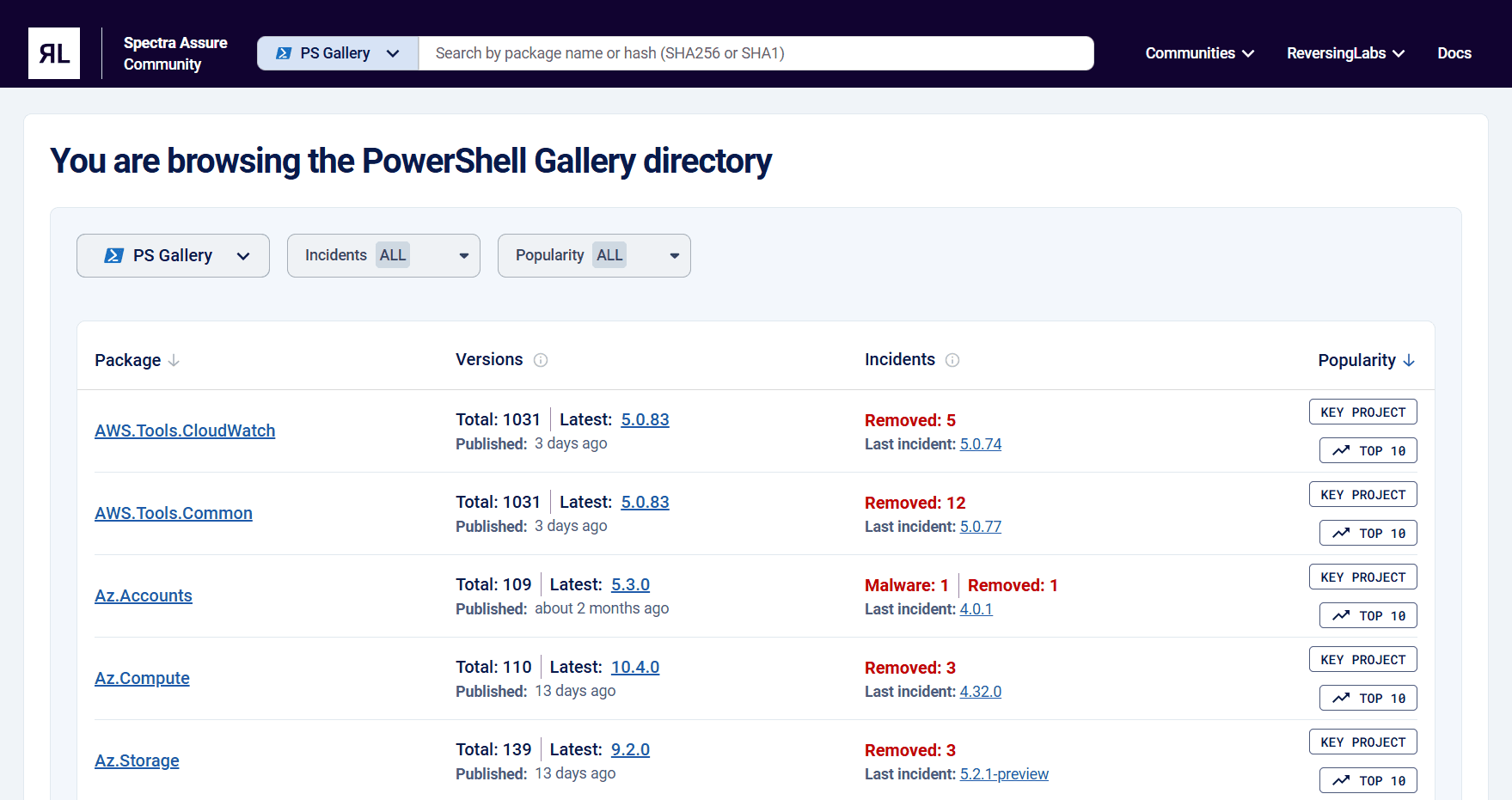
Figure 1: Review software supply chain risks before using PowerShell Gallery modules with Spectra Assure Community.
Newer doesn't always mean safer when it comes to software and its dependencies, regardless of whether it is used during development, in production environments or for automation purposes. The rapid spread of updated npm packages compromised by the Shai-hulud worm demonstrated why it is important for organizations to incorporate a verify first approach for updating automation modules.
Using Spectra Assure Community dramatically simplifies the process of making informed decisions about version upgrades. ReversingLabs continually assesses new module versions as they are published to the public repository with automated threat hunting analysis to flag changes that are malicious or seem suspicious and a dedicated research team to validate the threat. Additionally, older versions of each package are rescanned regularly, checking for emerging threats or newly reported vulnerabilities across the whole package history.

Figure 2: Spectra Assure behavior-based analysis provides early warning of emerging threats.
With Spectra Assure Community, PowerShell Gallery users now have more insight for choosing modules to automate their workflows while mitigating software supply chain risks. See RL's guided tour (view time: 60 seconds) to learn how the Spectra Assure Community helps you make the best choices for keeping your credentials, projects and end-users safe from malicious attacks.

The new landscape report maps 35 vendors addressing an emerging category of risk: AI agents writing insecure code at machine speed.

RL threat detection and binary analysis can now close the gap for threat hunters.

ReversingLabs joined defensive teams with its malware analysis platform. Here are key lessons.
Learn how to use ReversingLabs’ Spectra Analyze to expand your detection of malicious Telegram C2 bots.
