Spectra Assure Free Trial
Get your 14-day free trial of Spectra Assure for Software Supply Chain Security
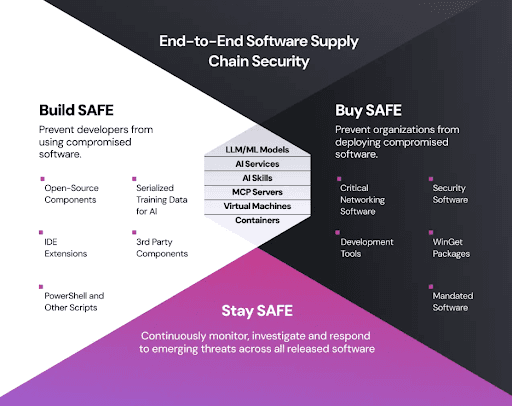
Get Free TrialMore about Spectra Assure Free TrialSoftware supply chain security is the practice of protecting software across its entire lifecycle from sourcing and development through build, packaging, and deployment to ensure it remains free from malicious code, tampering, and vulnerabilities. It validates both the components that go into software and the processes used to create and deliver software, covering third-party, open-source, and internally developed software along with the pipelines and infrastructure that connect them. The goal is to verify that every software artifact is authentic, secure, and compliant before it is published to the open market, delivered to customers, or deployed in production.
Modern applications are built largely from third-party and open-source components, assembled through automated pipelines across distributed teams. This accelerates delivery but dramatically expands risk because hidden malicious artifacts can then be introduced anywhere along the development process, such as when coding begins, when components are updated, during software compilation, and during packaging for delivery. Compiled malicious artifacts bypass traditional source-code scanning, and a compromised pipeline can propagate attacks at scale to impact hundreds to thousands of organizations. The software supply chain is now one of the most targeted areas in cybersecurity, and the rapid growth of AI-assisted coding is amplifying the security gaps further.
Beyond the immediate security threats, a compromised software supply chain creates significant business risks. It exposes organizations to data breaches, theft of valuable intellectual property, regulatory non-compliance, and loss of customer trust. When an organization falls victim to a software supply chain attack, customers question whether their data is adequately protected, driving them toward competitors. Robust supply chain security measures are therefore essential for maintaining regulatory alignment, protecting sensitive assets, and preserving the trust that customers and stakeholders place in your organization.
The key stakeholders involved in the software supply chain include open source maintainers, open source stewards, software publishers, and software buyers. Learn more in this OpenSSF Europe speech)
Effective software supply chain security requires layered controls across the entire SDLC, not just at the point of code creation. Organizations must implement controls at multiple stages to address threats as they emerge throughout the development and deployment process.
Implementing a comprehensive software supply chain security strategy delivers measurable value across your entire organization. By establishing robust controls and visibility throughout your development lifecycle, you gain the ability to identify and address threats before they impact production systems.
Organizations that invest in SSCS experience:
Software supply chain security provides multiple mechanisms to prevent and detect attacks across different stages of development and deployment.
Key defense mechanisms include:
Learn how Spectra Assure helps secure your software supply chain →
Software supply chain security addresses multiple business and technical requirements across different organizational contexts and roles.
Common applications include:
These findings underscore the urgent need for enhanced software supply chain security measures across all sectors. For a comprehensive analysis and more detailed insights, read the full State of Software Supply Chain Security 2026 report.
The 2020 SolarWinds cyberattack marked a significant turning point in how organizations view software supply chain security. This attack, part of a broader campaign targeting the software supply chain, brought to light the vulnerabilities that can exist within even the most trusted software providers. The repercussions were widespread, affecting both government agencies and private companies, and highlighting the urgent need for stronger security measures.
Following SolarWinds, the discovery of the Log4Shell vulnerability in the Log4j2 open-source library in 2021 reinforced the reality of software supply chain risks. This vulnerability demonstrated that these threats are not just theoretical; they pose real and significant dangers that require immediate and ongoing attention from organizations across all sectors.
While these recent events have drawn considerable attention to the issue, it’s important to recognize that software supply chain attacks are not a new phenomenon. Such attacks have been occurring for years, albeit with less visibility and urgency. The heightened awareness and response today reflect the growing complexity of the software ecosystem and the increasing reliance on third-party components.
In response to these evolving threats, organizations are now prioritizing software supply chain security by implementing rigorous protocols such as thorough code verification, continuous monitoring, and stringent supplier vetting. These measures are critical in mitigating risks and protecting against future attacks.
Trust must be continuously verified, not assumed at intake and extended indefinitely. Binary-level threats require capabilities beyond source-code-only tools. Automation is essential because manual review cannot scale to modern dependency volumes. Effective programs combine onboarding controls, build validation, artifact analysis, and continuous monitoring into a single, coherent strategy.
For further insights into software supply chain security, explore the following articles etc.:

This TeamPCP attack is a serious wakeup call about software supply chain security — and the problems with implicit trust.

Learn how attackers are re-casting adults as minors to bypass recovery and lock users out.

RL threat detection and binary analysis can now close the gap for threat hunters.