2025 DBIR & Third Party Breach Risk: A Conversation with Verizon

How to Get Your Software Vendors to Fix Their Code
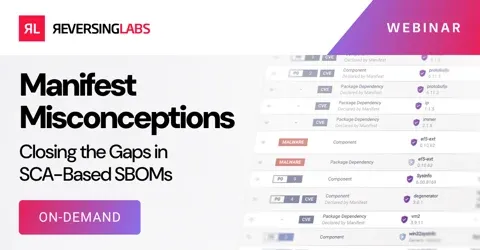
Manifest Misconceptions: Closing the Gaps in SCA-Based SBOMs

Securing Open Source and the Software Supply Chain: Addressing DORA, CRA, and NIS2

Ship Fast, Stay Secure: The Developer's Guide to Productivity

YARA Rules 201: Cross-Platform Detection Techniques

3 Questions You Should be Asking About Suspicious Files