Spectra Assure Free Trial
Get your 14-day free trial of Spectra Assure for Software Supply Chain Security
Get Free TrialMore about Spectra Assure Free Trial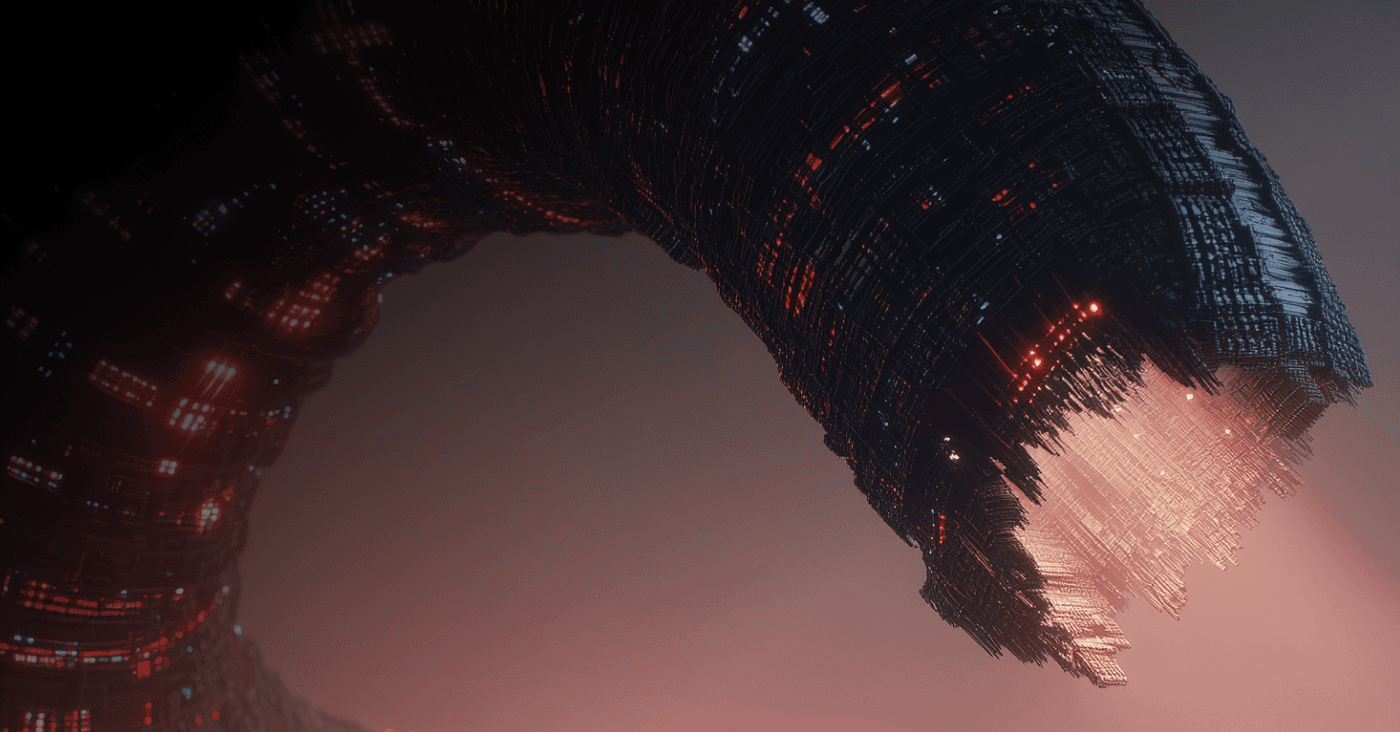
Mini Shai-Hulud, a software supply chain threat first detected in April, re-emerged on Monday, compromising more than 160 npm open-source software (OSS) packages, many of them popular and widely used with millions of weekly downloads.
The latest outbreak comes two weeks after the first “Mini Shai-Hulud” campaign first appeared, with compromises of widely used SAP Cloud Application Programming (CAP) and Cloud MTA Build Tool npm packages, among others, underscoring the growing threats to software supply chains.
Here’s what the ReversingLabs (RL) threat research team knows about Mini Shai-Hulud — and some key responses your team can take.
[ Learn about Spectra Assure Community | Join for free ]
The newest wave came into focus after the compromise of 84 malicious package versions tied to the widely used TanStack ecosystem. In its official post mortem, the TanStack team disclosed that attackers published malicious versions of 42 @tanstack/* packages to npm after the threat actors successfully compromised publishing credentials. The breach includes packages like @tanstack/react-router which has more than 12 million weekly downloads.
Tomislav Peričin, ReversingLabs co-founder and chief software architect, said TeamPCP, which is behind the latest attack, was targeting strategic open-source assets.
“That's not a niche library, it's load-bearing infrastructure for huge swaths of the JavaScript ecosystem, consumed directly and transitively.”
—Tomislav Peričin
TanStack said the malicious packages included credential-stealing functionality targeting developer environments and CI systems. The compromise highlighted a now-familiar pattern in software supply chain attacks, with trusted packages weaponized to harvest tokens and secrets that can then be used to compromise additional packages and organizations.
Security researchers say the attack appears linked to the broader Mini Shai-Hulud malware campaign first observed earlier this year, with a much broader scope. The security firm Aikido said its malware team identified “373 malicious package-version entries across 169 npm package names.”
Despite a broader range, the Mini Shai Hulud campaign’s objectives are consistent with earlier outbreaks. Attackers compromise developer environments with the goal of stealing credentials, and abusing trusted publishing workflows to spread further within compromised environments.
While most of the affected packages are on the npm open-source repository, the ripple effects of the attack stretch far beyond npm. On Monday, the Guardrails AI project acknowledged that malicious activity linked to the campaign affected components within its ecosystem as well.
The worm-like behavior of the campaign hinges on harvesting developer and automation secrets from infected systems and then using those credentials to publish additional malicious packages, The Hacker News reported.
That behavior closely mirrors the original Shai-Hulud worm documented by ReversingLabs researchers in 2025. RL researchers observed how Shai-Hulud systematically harvested npm tokens, GitHub credentials, and cloud provider secrets from compromised developer environments using tools like TruffleHog. The malware then leveraged those credentials to tamper with additional packages and repositories, effectively turning the software supply chain itself into a propagation mechanism.
As RL explained in its Shai-Hulud FAQ and analysis, the campaign represents a dangerous evolution in open-source malware. Rather than relying on developers to mistakenly install typo-squatted packages, the attackers compromised legitimate and highly trusted packages directly.
The latest Mini Shai-Hulud activity reinforces a broader trend RL has documented in recent Software Supply Chain Security Reports: attackers are increasingly targeting the infrastructure and trust relationships that underpin open-source ecosystems rather than simply exploiting software vulnerabilities. RL’s 2026 report notes that npm accounted for nearly 90% of detected open-source malware in 2025 and highlights how campaigns like Shai-Hulud weaponized stolen credentials to spread at scale.
The campaign also demonstrates how exposed development secrets continue to fuel software supply chain attacks. RL researchers have repeatedly shown that leaked npm tokens, GitHub personal access tokens, cloud credentials, and CI/CD secrets remain widely available across open-source ecosystems.
For software teams and developers whose environments may have touched any compromised package versions, the response should be immediate and aggressive:
Organizations should also review publishing workflows, implement short-lived credentials where possible, enforce MFA across package registries and source control platforms, and continuously monitor software artifacts for tampering and unauthorized changes.
The RL threat research team is continuing to monitor open-source registries as this campaign evolves.