
Digital Certificates – Models for Trust and Targets for Misuse 1
Blog 1: Building secure certificate whitelists

Blog 1: Building secure certificate whitelists

Operation ShadowHammer is a new and highly targeted supply chain attack discovered by Kaspersky Lab.

Guest blog by Edvard Amoroso, Founder and CEO of TAG Cyber
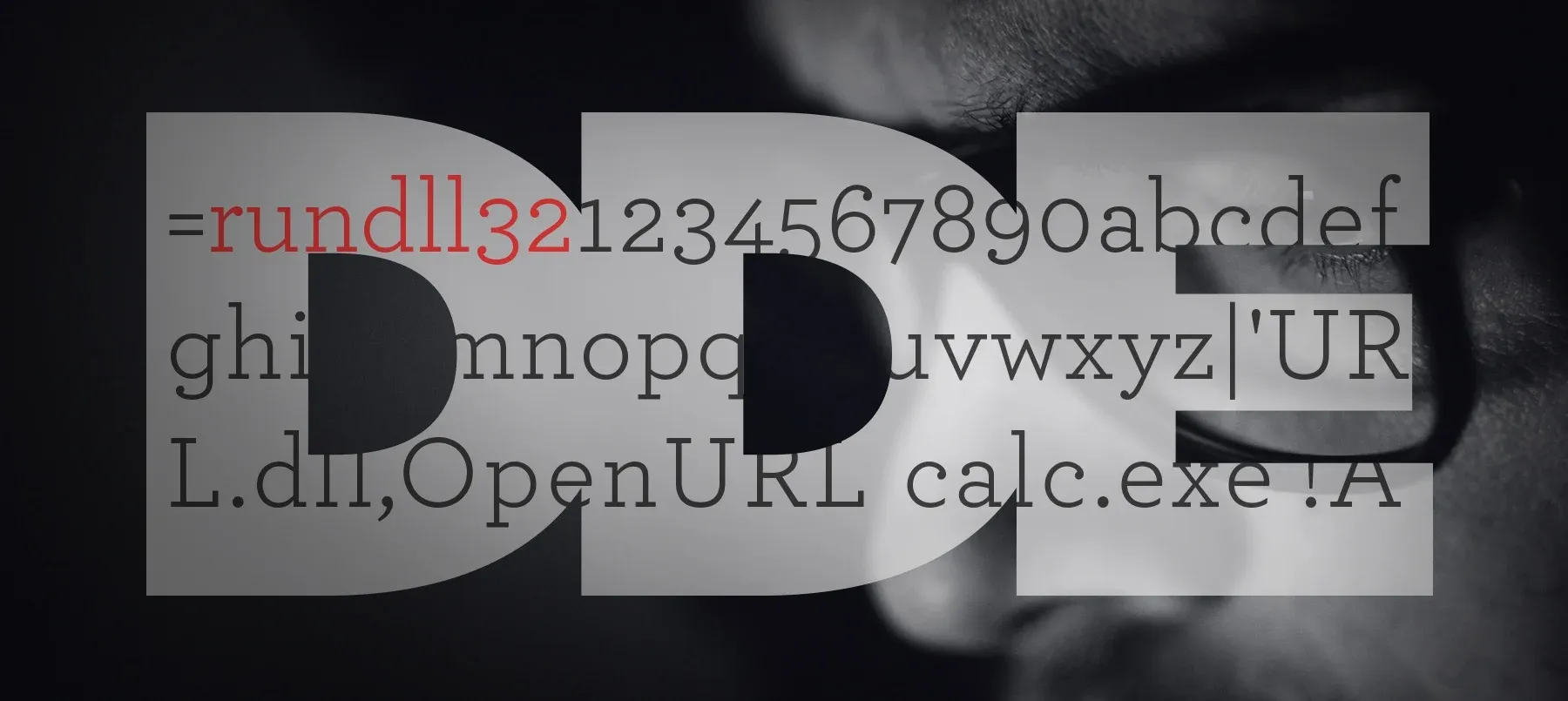
The natural order of things is to evolve, so it was just a matter of time until obfuscations and variations would start appearing in the wild.

Join ReversingLabs Research on a Threat Hunt for revoked D-Link certificates

A 17-year-old vulnerability in Microsoft Office Equation Editor is now confirmed to be exploited by the Cobalt Group

BadRabbit a previously unknown ransomware family which started spreading on October 24th

One constant challenge of modern security will always be the difference between published and implemented specifications.

Learn how to do in depth analysis of compressed and encrypted binary files.

Reverse engineering compressed binaries has been a necessity for more than a two decades now, and we as reverse engineers are always on a lookout for newest and fastest ways of accomplishing our goal.
Get your 14-day free trial of Spectra Assure for Software Supply Chain Security
Get Free TrialMore about Spectra Assure Free Trial